Take a tour












All Demos
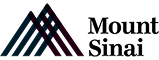
PCI DSS Key Management
Meeting PCI DSS requirements demands robust key management. This demo illustrates how you can use AQtive Guard filtering to efficiently identify and prioritize cryptographic key vulnerabilities, so you can protect payment card data and maintain continuous compliance.
Impact Assessment for Crypto Migrations
Let's explore the AQtive Guard Impact Assessment feature, engineered to give you that confidence.
Getting Started: Security Knowledge Graph
Learn how the AQtive Guard Security Knowledge Graph provides a visual map of your security landscape and enables you to explore connections interactively.

Understanding Enrichments: Reducing False Positives
We'll show you how AQtive Guard data Enrichments helps you cut through this noise to focus on what truly matters for your security.
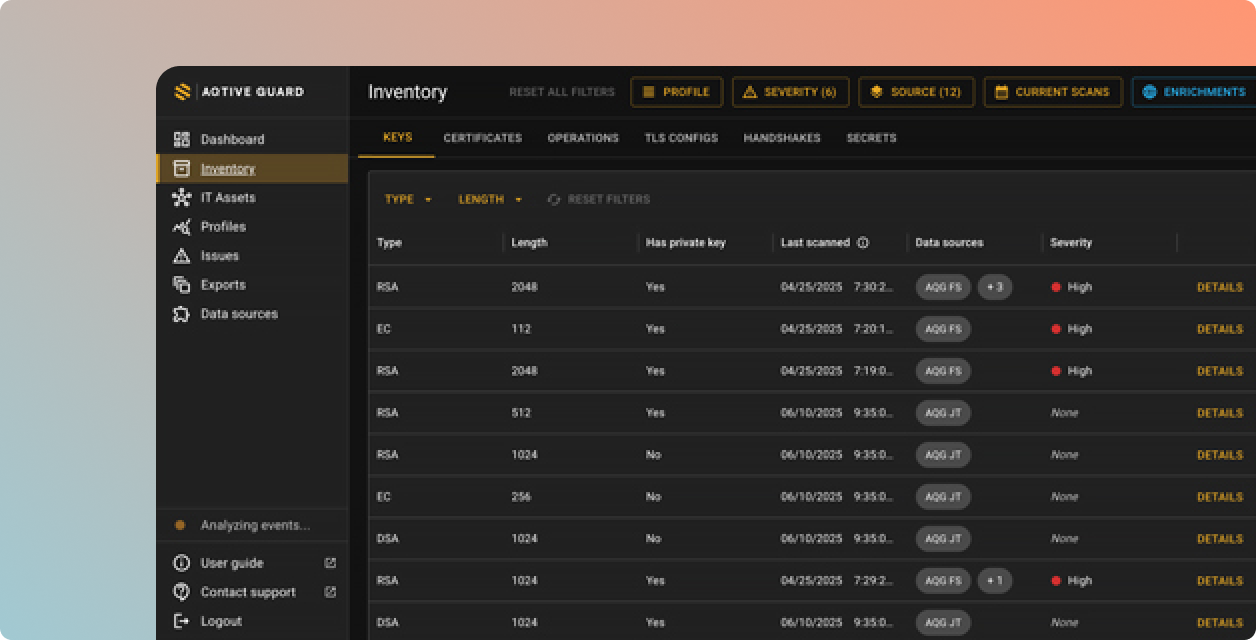
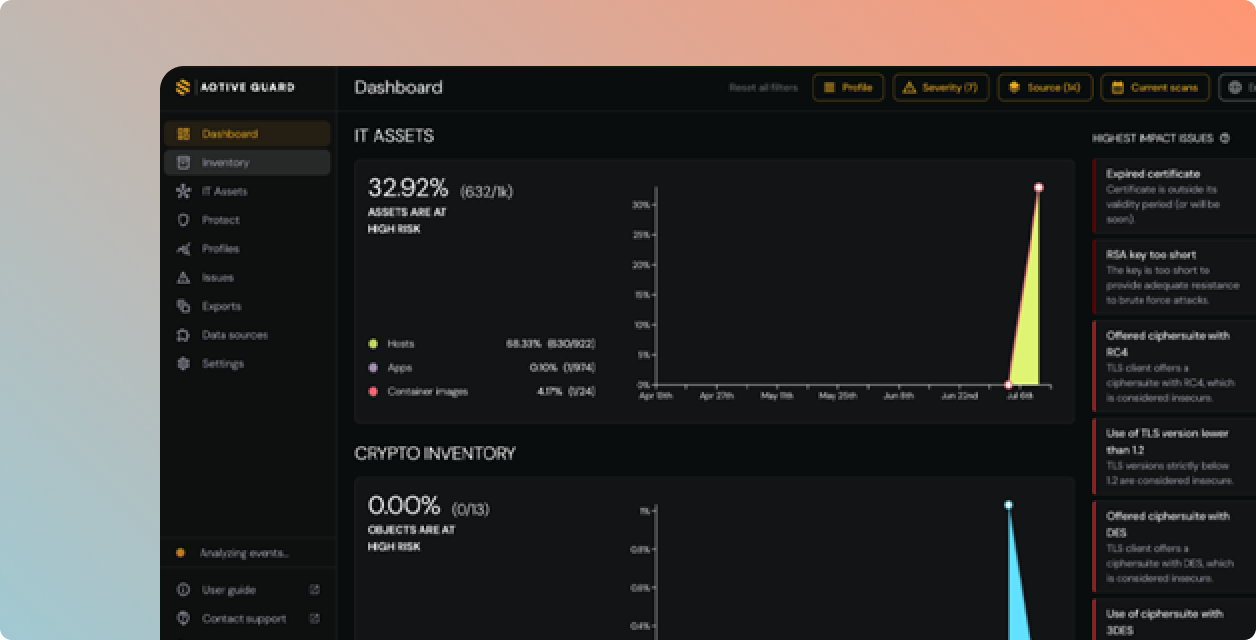
What makes AQtive Guard different.
Live runtime context, not just static scanners
Don't just see where cryptography exists, see how it's actually being used. Network analysis and runtime tracing reveal what's actively running in production. We give you the context to prioritize real risk.
Standard authors, not just spec readers.
Our cryptographers didn't just read the NIST PQC standards, they assisted in developing them. AQtive Guard is not just buying another security scanner; it’s built by the team that wrote the cryptographic blueprint for the post-quantum future.
Impact simulation, not change anxiety.
Go beyond dashboards and noisy alerts. AQtive Guard combines regulatory risk with business context to simulate the blast radius of changes before you make them. Implement safe key rotation, algorithm replacement, and PQC migrations with absolute evidence, without breaking production.
Fast time-to-value.
Minimal overhead.
AQtive Guard is a SaaS platform. Sensors push data via encrypted channels, and third-party integrations connect via secure APIs. Most teams see their first results within hours of connecting a data source.
Unified sensor grid covers both AI discovery and cryptographic inventory
Cloud-native deployment on AWS, Azure, and GCP
Agentless cloud scanning via IAM roles
Browser sensor for real-time employee AI usage visibility
Seamless integrations with your security stack
Secure AI & Cryptography
Complete visibility into every AI system, correlated risk context, runtime enforcement, and compliance reporting, in one platform.
agent, and MCP server.