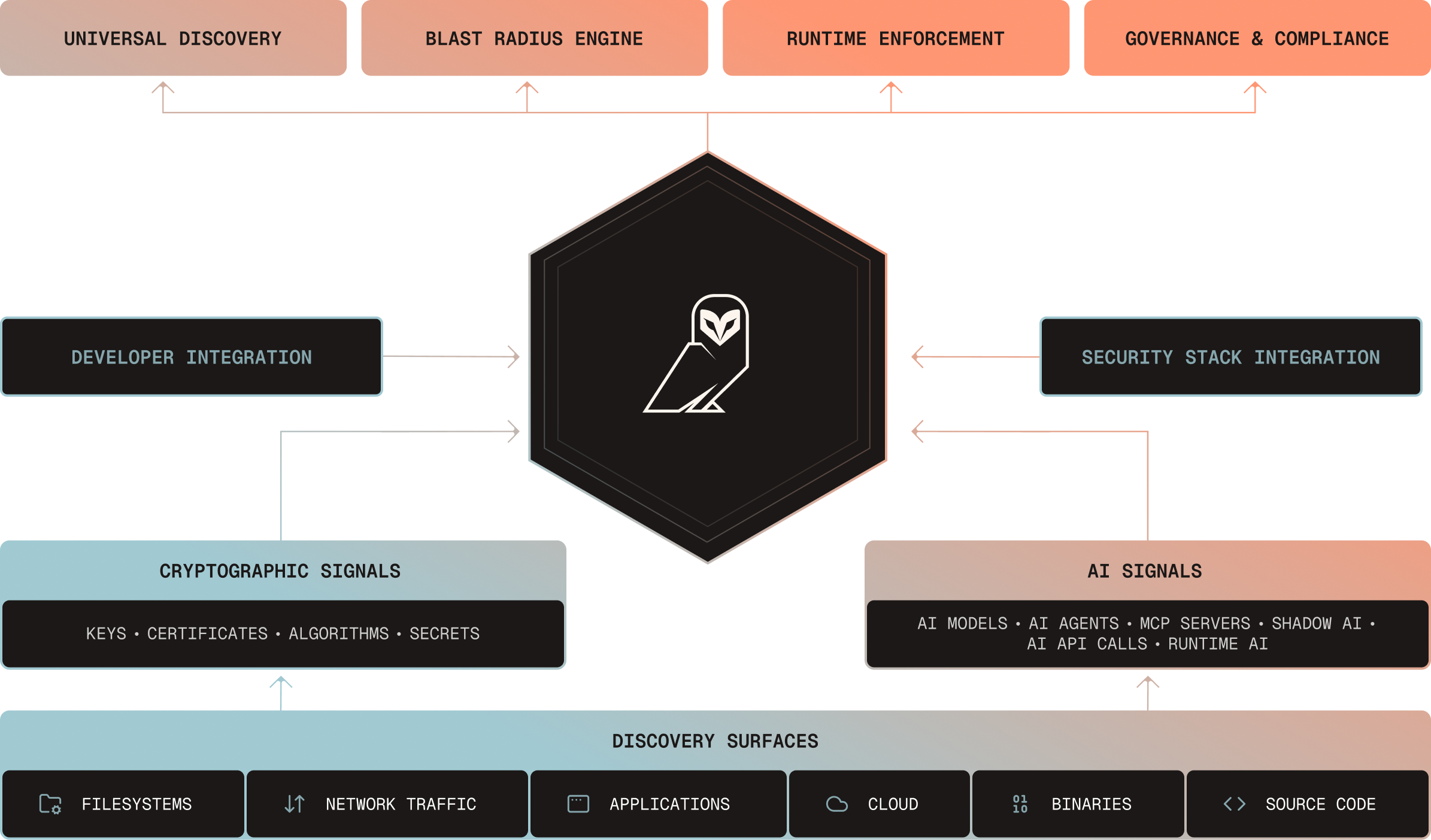
One control plane for your most critical invisible risks.
A unified platform designed to enable machine trust at scale. AQtive Guard discovers hidden AI and cryptographic assets, maps their blast radius, and enforces machine-speed remediation, all from a single deployment.












Four stages. One continuous loop.
Every AI and cryptographic asset flows through this lifecycle – automatically and continuously at scale.
See every AI system and cryptographic asset in use.
Six scanning surfaces.
Prioritize what
actually matters.
Security Knowledge
Graph correlation.
Turn AI and crypto risk into
auditable evidence.
Compliance dashboards.
Enforce policy and fix issues at machine speed.
Inline enforcement.
Using the AQtive Guard
Loop to Achieve End-to-End
AI & Cryptographic Security.
AQtive Guard is a unified platform that delivers complete visibility, contextual risk analysis, active enforcement, and audit-ready compliance across your entire AI and cryptographic landscape.
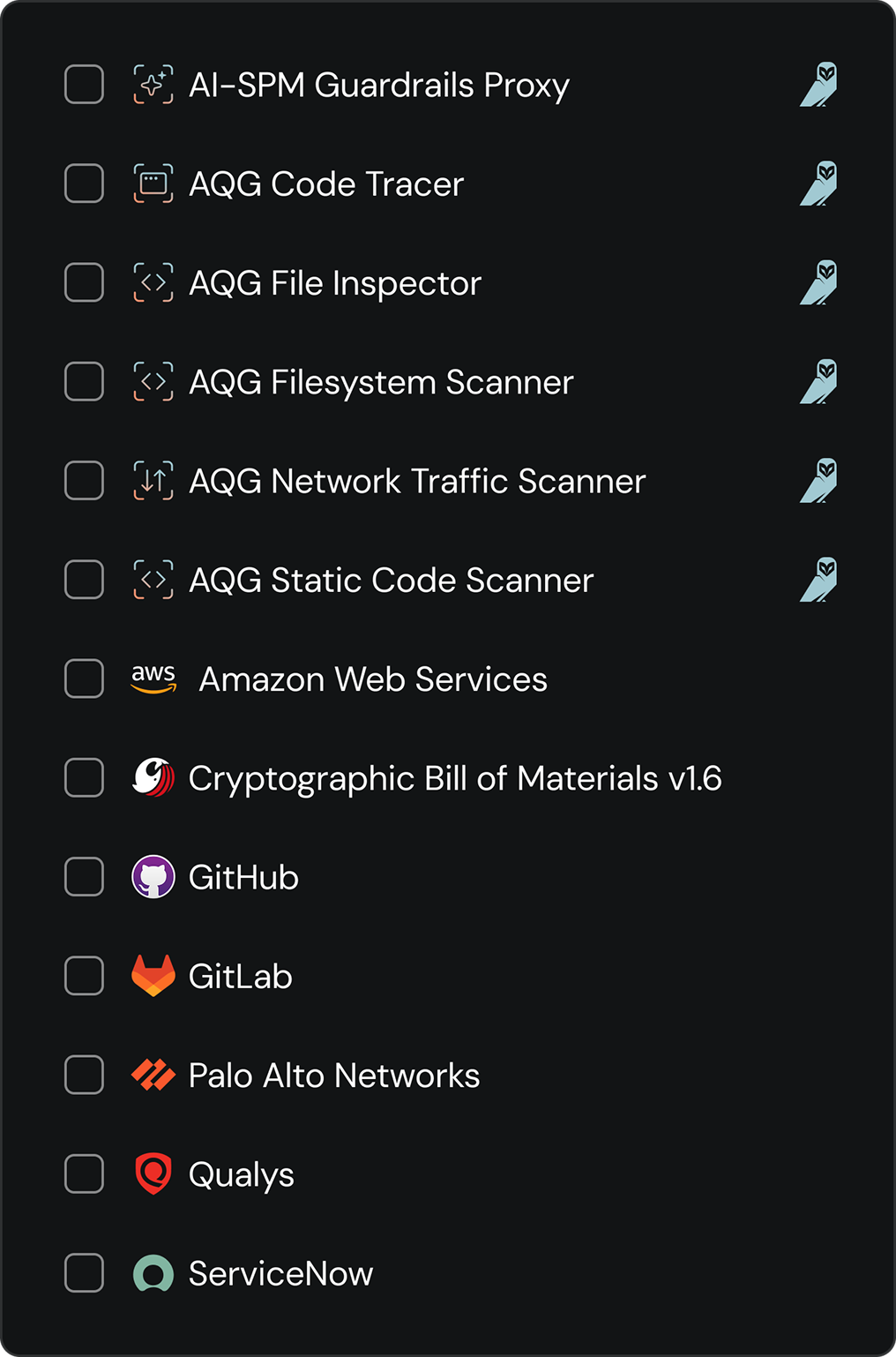
Six surfaces. One deployment.
Purpose‑built sensors for each environment feed into a single correlation engine. Whether it’s tracing an AI model in a browser or a deprecated cryptographic algorithm in a live network, AQtive Guard gives you complete visibility without forcing you to buy fragmented tools.
One deployment covers AI and cryptographic inventory — complete visibility without separate tools or manual audits.
Six surfaces. One deployment.
Scan source code, CI/CD pipelines, container images, and binaries. Detects AI model imports, API keys, and cryptographic library usage.
Analyze live traffic for AI API calls, TLS handshakes, and data flow patterns.
Lightweight scanner on servers, laptops, and workstations. Detects locally installed AI tools and cryptographic configurations.
Agentless scanning via IAM roles for AWS, Azure, and GCP. No sensor deployment needed.
Real-time visibility into third-party AI tools employees use such as ChatGPT, Copilot, Gemini, or other web-based AI services.
Deep runtime inspection of AI processes in memory. Detects model loading, inference execution, and runtime behavior.
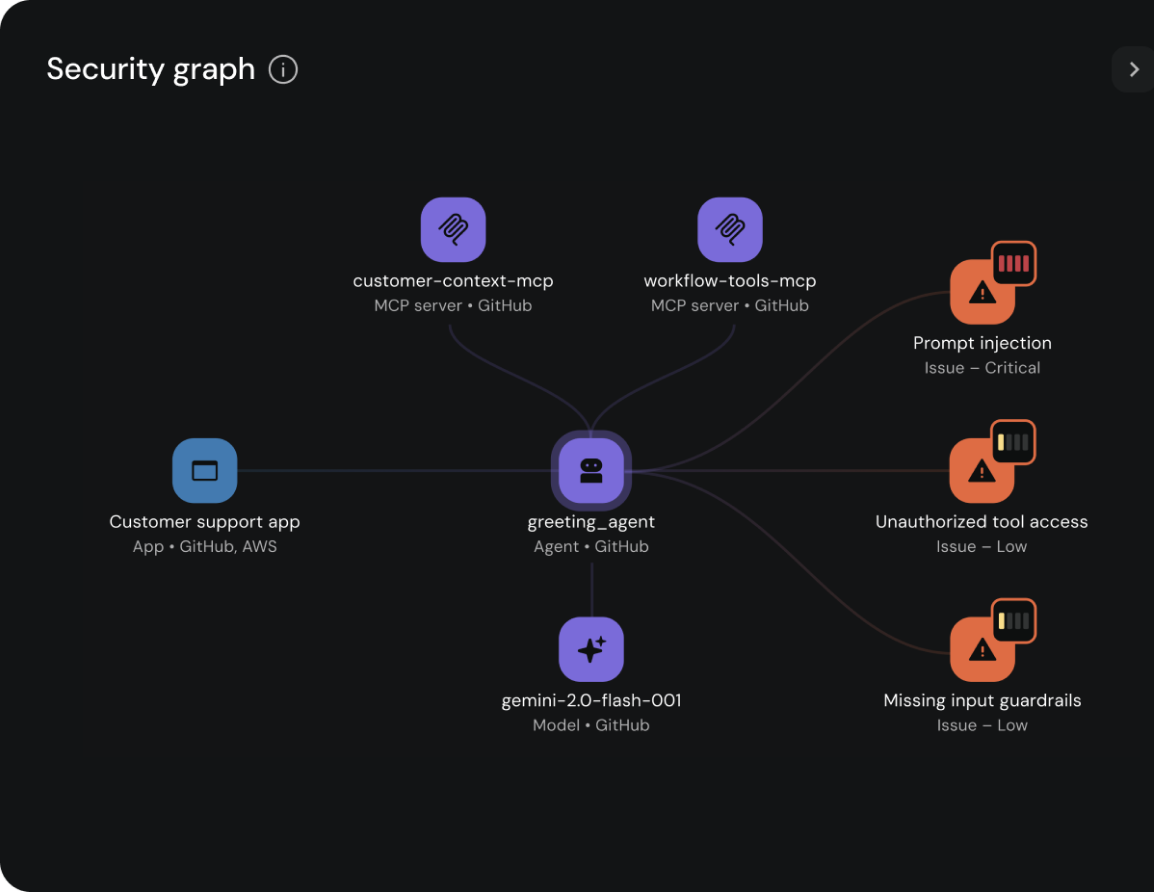
How we turn signals into context.
AQtive Guard maps every discovered asset to its infrastructure, owners, permissions, and related issues. Investigations that took days collapse to minutes.
See the exact blast radius of a vulnerability instantly, without chasing signals across fragmented tools.
What we connect
Where it lives, what it is, and its cryptographic posture.
Who owns it, who uses it, and what data it touches.
Is it exploitable? What is the business criticality? What breaks if we change it?
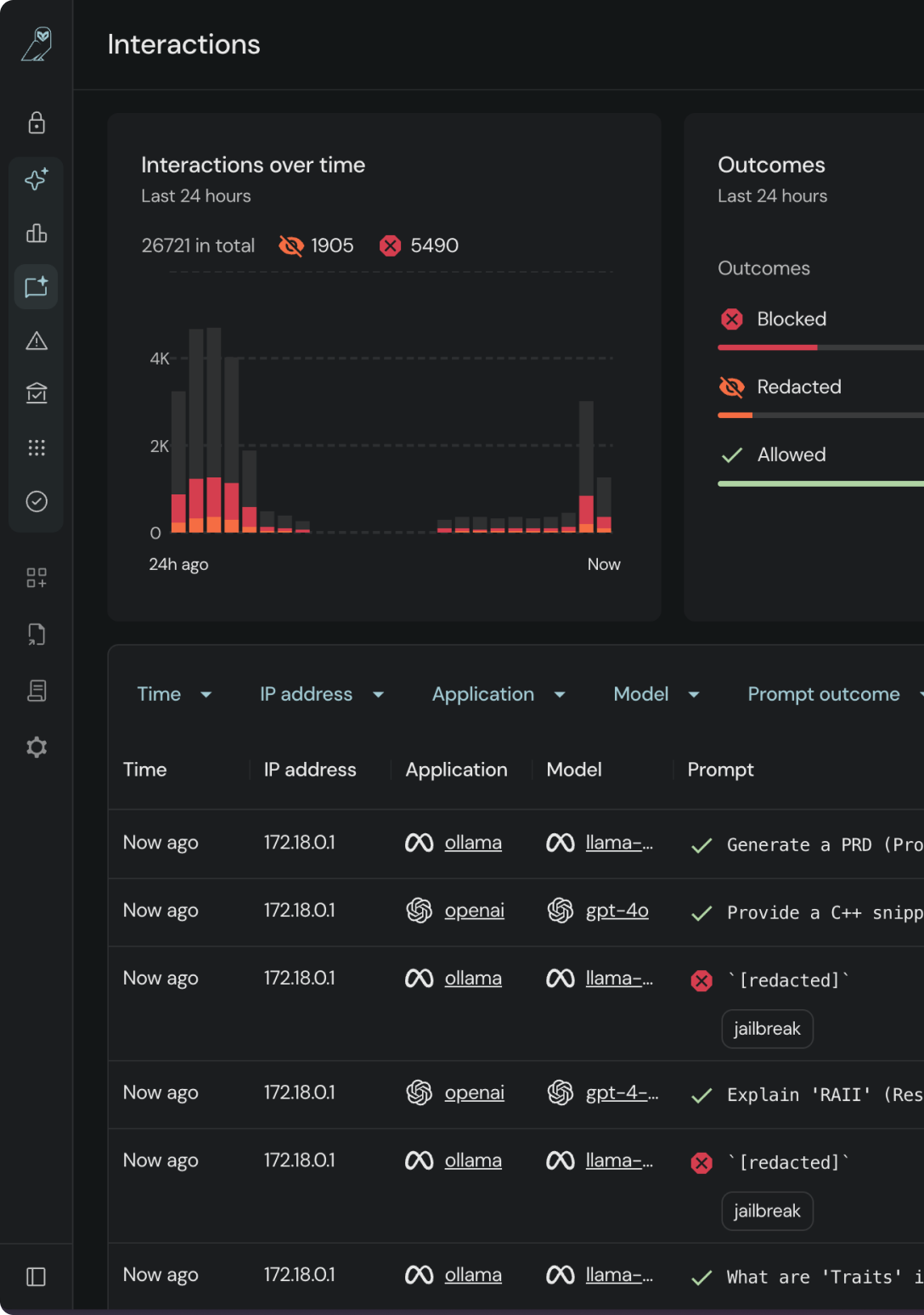
Runtime guardrails. Automated orchestration.
Stop relying on passive alerts. AQtive Guard bridges the gap between detection and resolution by actively enforcing AI policies and safely orchestrating cryptographic changes, without adding latency or breaking production.
Ship AI faster and eliminate change anxiety. Empower your teams to move at machine speed without security acting as a manual roadblock.
What gets enforced
AI Runtime Guardrails
Malicious instructions are stripped before reaching the model.
Crown-jewel policies prevent source code, credentials, or PII from leaking to public LLMs.
Employees using Shadow AI are automatically redirected to approved, corporate-secured alternatives.
Cryptographic Orchestration
Automate the rotation of expired certificates and stale keys without guessing what will break.
Safely replace deprecated algorithms and quantum-vulnerable ciphers using context-aware impact simulation.
Automatically block the deployment of deprecated algorithms (MD5, SHA-1), short keys, and unauthorized ciphers.
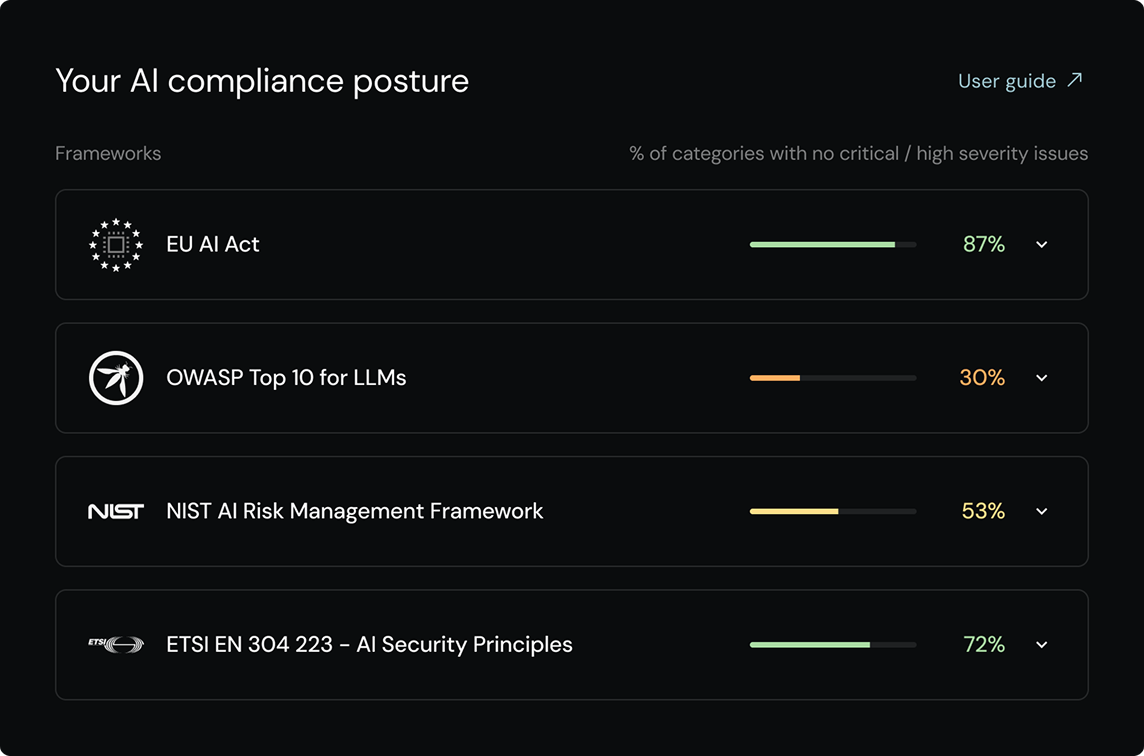
Audit-ready. Always.
Dashboards map your posture to the frameworks that matter, AI governance and cryptographic standards.
When the board asks for support or an auditor requests your data, you're ready without scrambling.
Supported Frameworks
Fast time-to-value.
Minimal overhead.
AQtive Guard is a SaaS platform. Sensors push data via encrypted channels, and third-party integrations connect via secure APIs. Most teams see their first results within hours of connecting a data source.
Unified sensor grid covers both AI discovery and cryptographic inventory
Cloud-native deployment on AWS, Azure, and GCP
Agentless cloud scanning via IAM roles
Browser sensor for real-time employee AI usage visibility
Seamless integrations with your security stack
See the platform in action.
Walk through the architecture, see real discovery results, and understand how AQtive Guard fits into your security stack.
Govern AI interactions.