The PQC Deadline is Coming
Gain cryptographic control. Reduce risk.
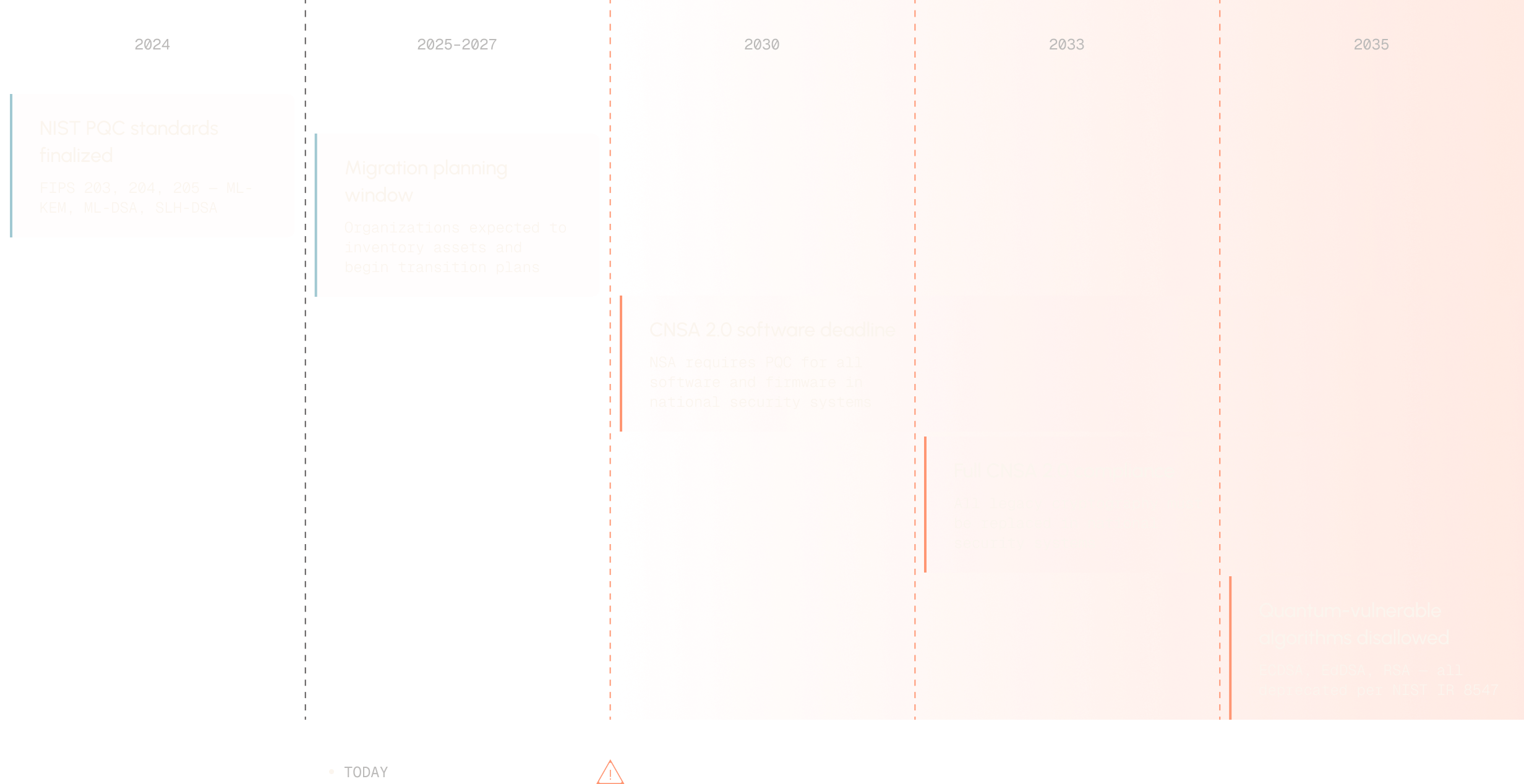
Compliance deadlines for CNSA 2.0, NIST, and federal PQC mandates are already here. AQtive Guard discovers every key, certificate, and cryptographic operation across your infrastructure, so you can remediate risk and address compliance obligations to auditors and boards.












Cryptographic risk isn't just a future problem. It's today's reality.
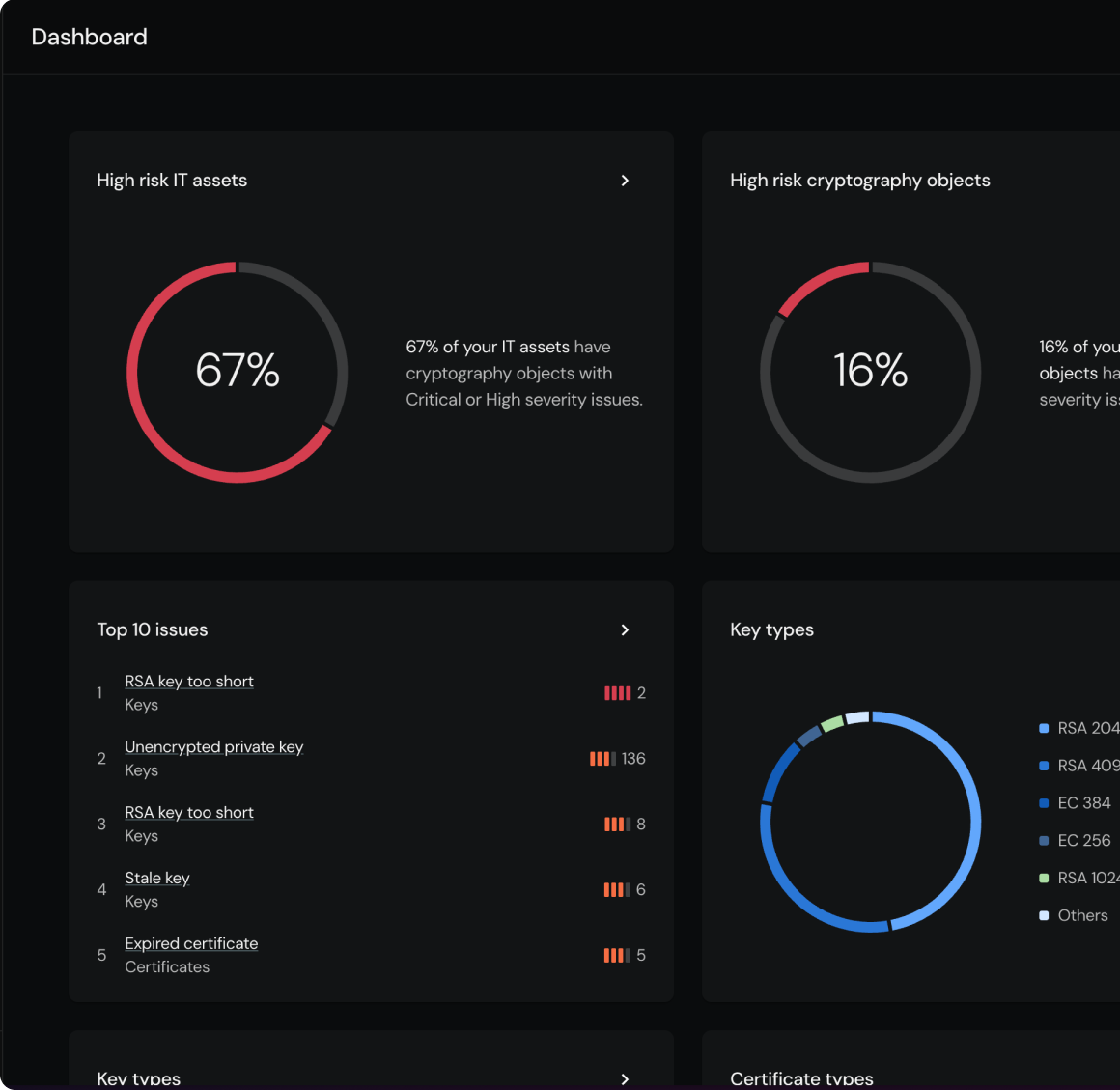
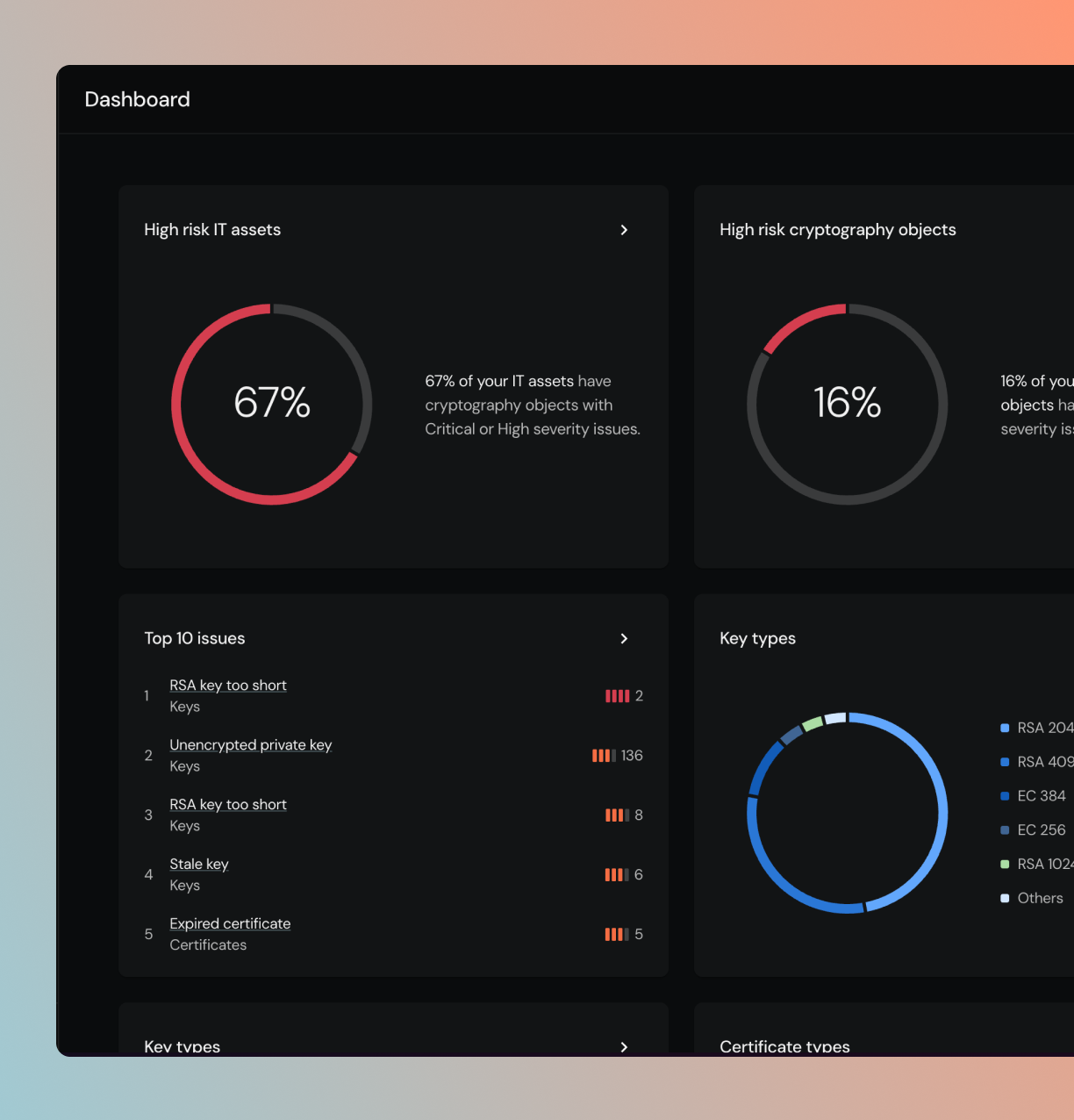
Weak, expired, and unmanaged cryptography is already exposing you.
Deprecated algorithms, expired certificates, short keys, and unencrypted private keys create real attack surface today — before quantum is even a factor.
PQC compliance deadlines are here.
Federal and industry mandates now require cryptographic inventories and PQC migration proof. Organizations that can't show progress face audit failures and lost contracts.
The post-quantum clock is ticking.
Before you can migrate, you have to answer one question: Where is our cryptography hiding?
End-to-end cryptographic management.
Most tools do one thing, manage certificates or scan static code. AQtive Guard bridges the gap between finding cryptographic assets, risk and fixing them by automating the full lifecycle in a single control plane.
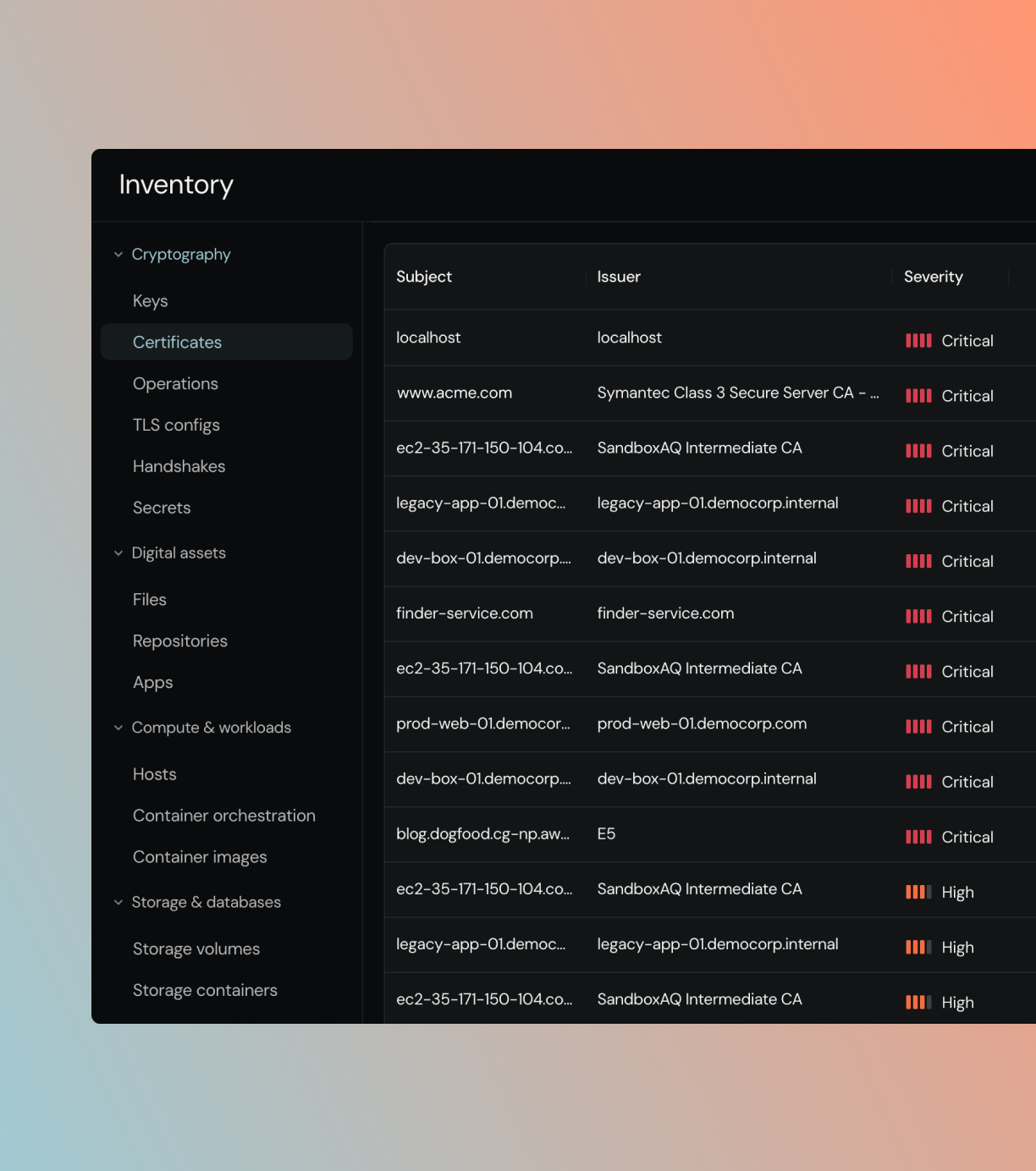
Universal cryptographic inventory.
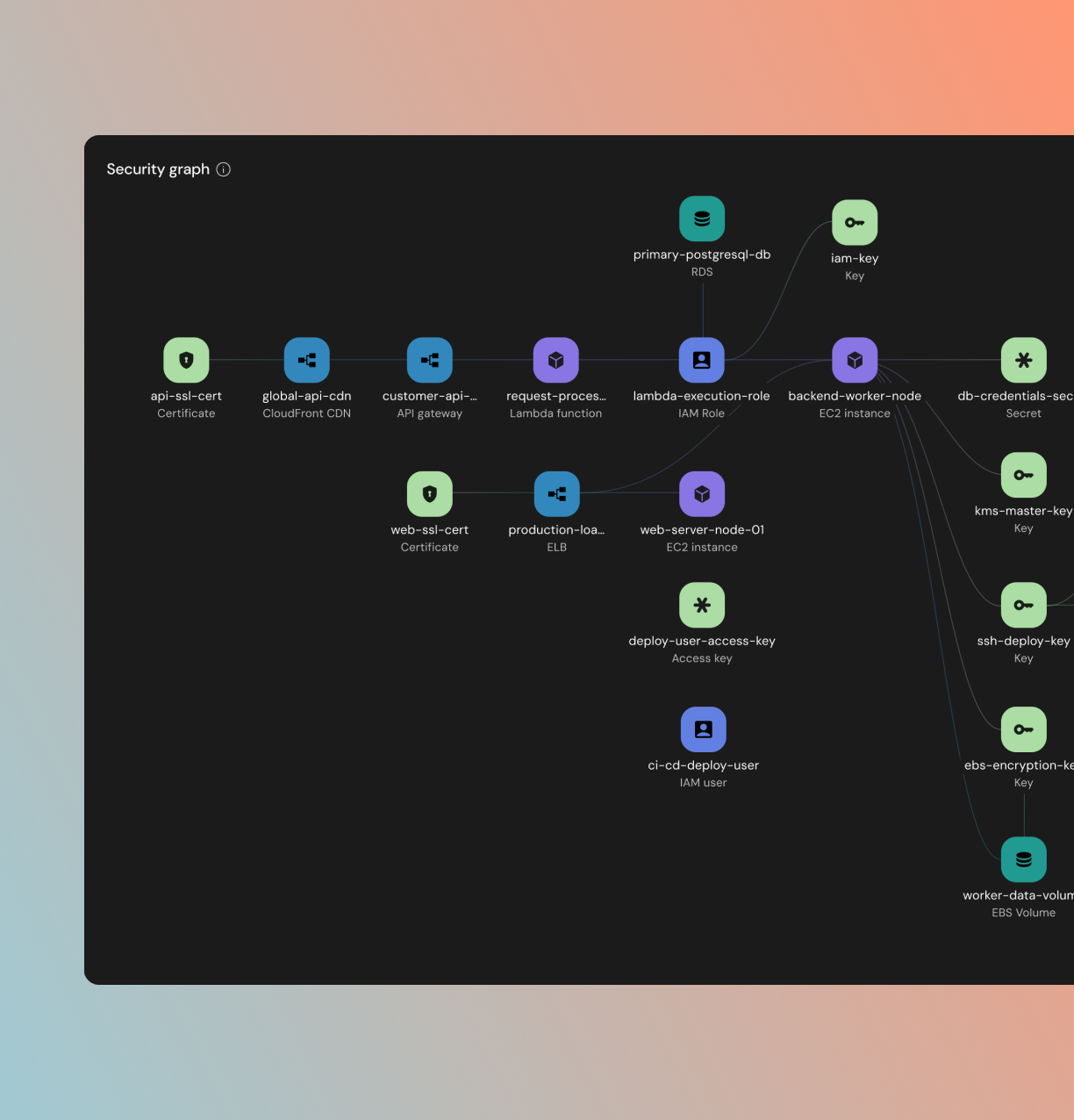
Legacy PKI tools only see what they manage. AQtive Guard correlates data across code, runtime, and the network. Discover every managed certificate, hidden algorithm, and shadow key with zero manual effort.
Context-aware risk.
See which cryptographic assets carry themost business risk. AQtive Guard maps everykey, certificate, and algorithm to its owners, dependencies, and blast radius, so you canprioritize what matters and remediate safely.
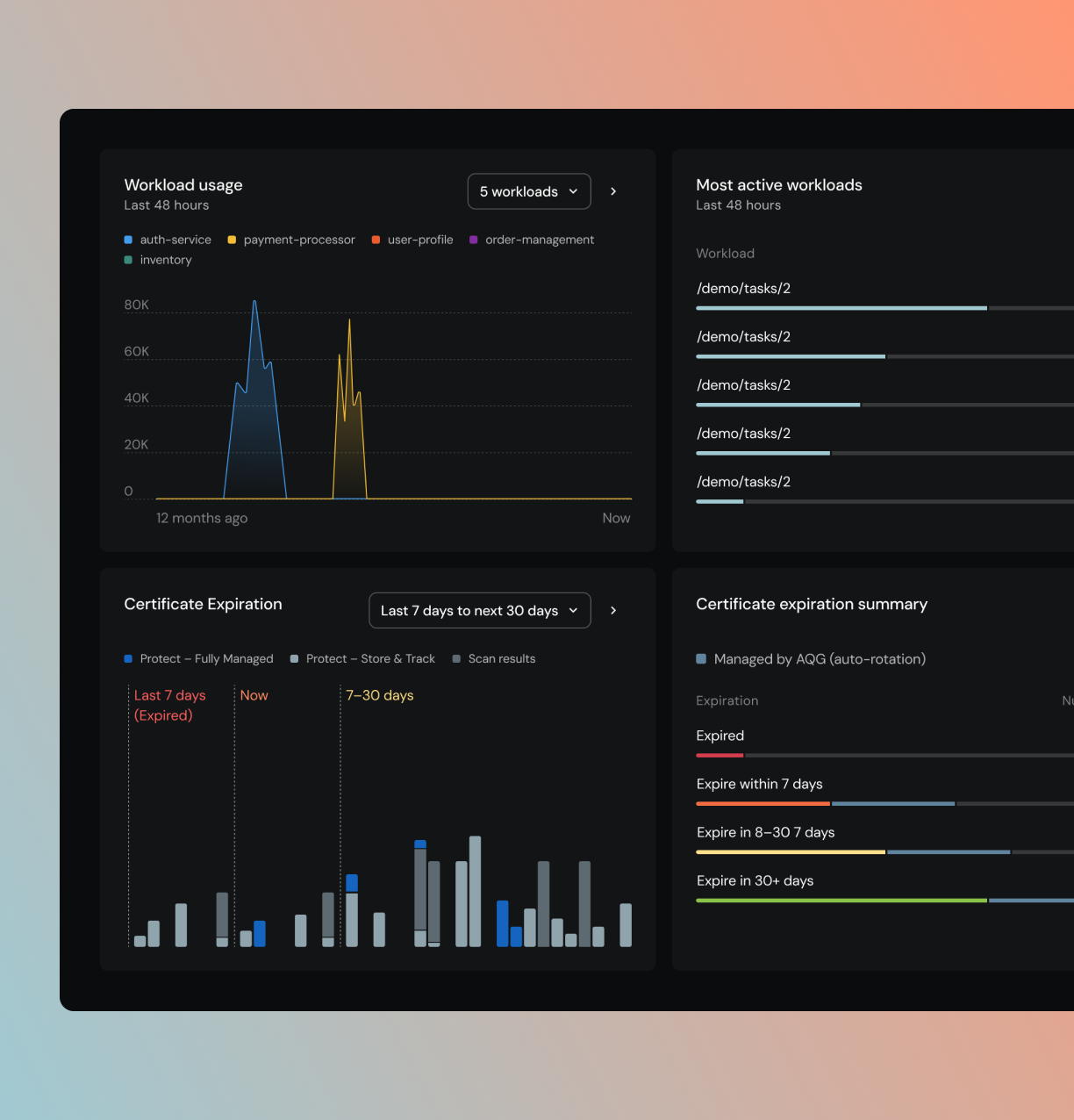
Active orchestration and remediation.
Certificate outages cost up to $9,000/minute. Eliminate change anxiety with impact simulation and risk scoring. Confidently orchestrate safe key rotations, algorithm replacements, and PQC migrations without breaking production.
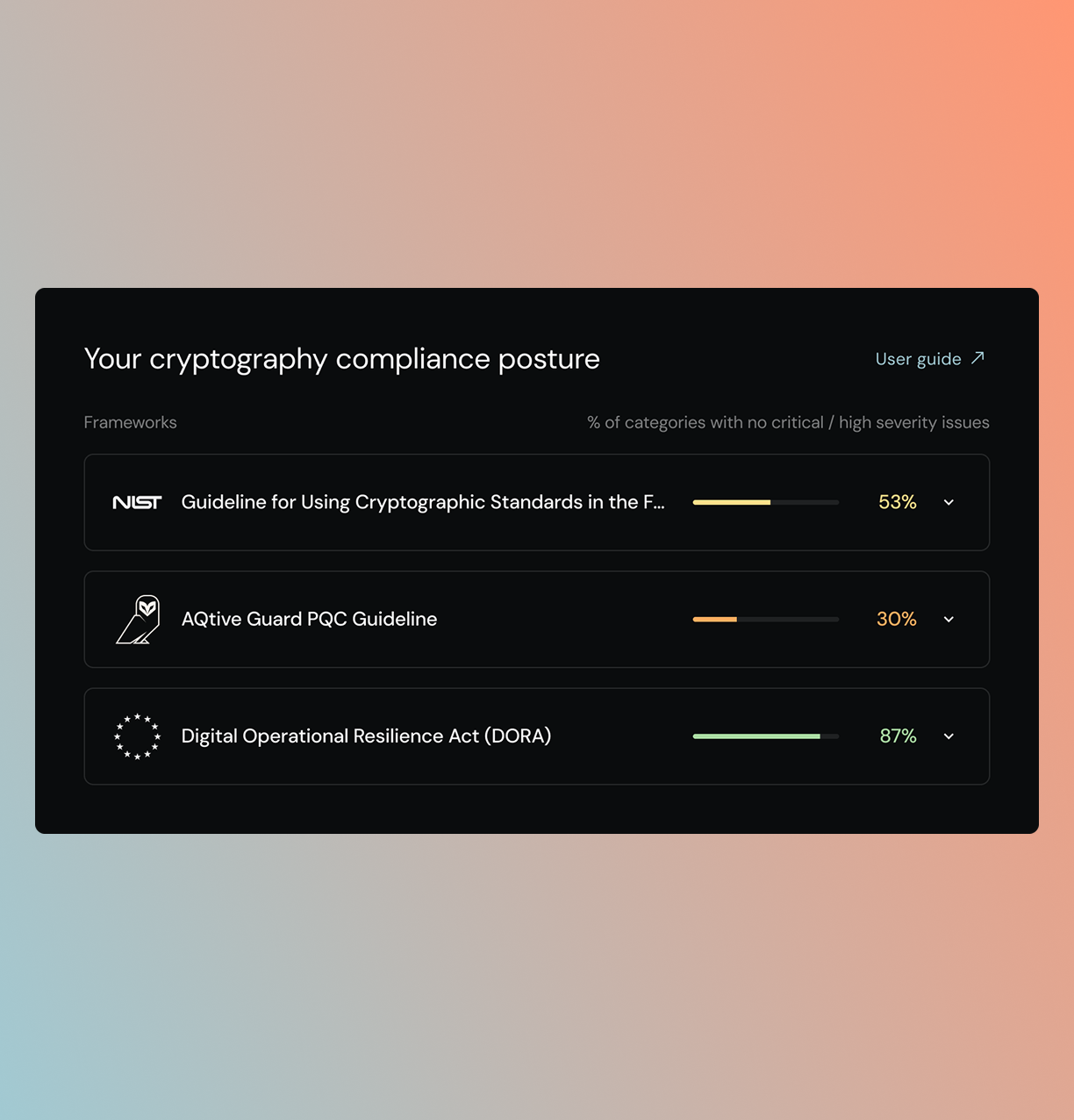
Policy-driven compliance and proof.
Continuous compliance tracking and exportable reporting. Generate complete Cryptography Bills of Materials (CBOMs) to prove progress against CNSA 2.0, NIST mandates, and internal security policies.
What makes AQtive Guard different.
Live runtime context, not just static scanners
Don't just see where cryptography exists, see how it's actually being used. Network analysis and runtime tracing reveal what's actively running in production. We give you the context to prioritize real risk.
Standard authors, not just spec readers.
Our cryptographers didn't just read the NIST PQC standards, they assisted in developing them. AQtive Guard is not just buying another security scanner; it’s built by the team that wrote the cryptographic blueprint for the post-quantum future.
Impact simulation, not change anxiety.
Go beyond dashboards and noisy alerts. AQtive Guard combines regulatory risk with business context to simulate the blast radius of changes before you make them. Implement safe key rotation, algorithm replacement, and PQC migrations with absolute evidence, without breaking production.
See all your cryptography. Not just what's in your PKI.
PKI and certificate lifecycle tools only see certificates they manage. AQtive Guard scans your entire infrastructure, filesystems, live network traffic, cloud configurations, code, and endpoints, finding keys, certificates, algorithms, and cryptographic operations.

What AQtive Guard Finds
Cryptography at rest
Keys in keystores, certificates in repos, algorithms in code. Static inventory of what exists across your infrastructure.
Cryptography in motion
Live TLS handshakes, runtime cryptographic operations, network cipher suites. See what's being used, when, and by whom, critical for prioritization.
Integrate with your existing security stack









Built for your role.
CISO
“The board wants a quantum readiness plan and I don’t have one."
Complete cryptographic inventory, quantum vulnerability assessment, and a concrete migration roadmap, with compliance dashboards for NIST PQC and CNSA 2.0 reporting.
Security Architect
“Legacy scanners only show me what's in our key vaults. I need to know what developers are actually running in production right now.”
Automated discovery across filesystems, network traffic, cloud, and code. Every key, certificate, and algorithm mapped, assessed, and prioritized, continuously.
Compliance & GRC
“I need automated, evidence-backed reporting to prove CNSA 2.0 and NIST compliance without interrupting engineering workflows.”
Evidence‑backed compliance mapping with exportable reports and impact assessments. Track migration progress against CNSA 2.0 milestones with concrete metrics.
Know what cryptography you're running. Fix what's broken.
Complete cryptographic inventory, vulnerability detection, and PQC migration planning, built by the researchers who contributed to the NIST standards.